Microsoft Entra and Identity Strategies for Azure Virtual Desktops
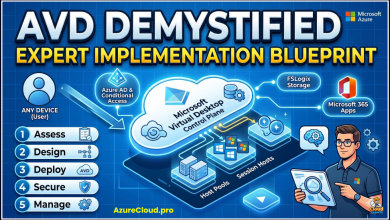
Configure Azure Virtual Desktop with the enterprise-grade configurations you’ll want in place for secure authentication, improved connectivity, flexible user data, and service resiliency.
 A key enterprise use for the Entra identity suite is the role it plays in enabling and managing Azure Virtual Desktops.
A key enterprise use for the Entra identity suite is the role it plays in enabling and managing Azure Virtual Desktops.
In this presentation Matt McSpirit explains how to configure Azure Virtual Desktop with the enterprise-grade configurations you’ll want in place for secure authentication, improved connectivity, flexible user data, and service resiliency.
- Your options using Azure Active Directory to achieve single sign on and passwordless authentication.
- The newest experiences for using Web Authentication (WebAuthn) to redirect additional authentication factors to local devices.
- RDP Shortpath to optimize connectivity to remote hosts.
- Your options for using FSLogix to manage profile containers.
- Architecting your Azure Virtual Desktop configuration for resiliency, and
- Using Confidential Computing virtual machines to meet even the highest security requirements
Documentation
As the documentation describes Azure Virtual Desktop uses Azure AD for identity and access management. Azure AD integration applies Azure AD security features, such as conditional access, multifactor authentication, and Intelligent Security Graph, and it helps maintain app compatibility in domain-joined VMs.
Azure Virtual Desktop supports different types of identities depending on which configuration you choose, and uses Azure role-based access control (RBAC) to control access to resources.
[box type=”info” align=”” class=”” width=””]
Knowledge Base
The Cloud Adoption Framework describes Identity and access management considerations for Azure Virtual Desktop:
- Deploy Azure AD-joined virtual machines in Azure Virtual Desktop: This article will walk you through the process of deploying and accessing Azure Active Directory joined virtual machines in Azure Virtual Desktop.
- Supported identities and authentication methods: This article provides a brief overview of what kinds of identities and authentication methods you can use in Azure Virtual Desktop.
- Configure single sign-on for Azure Virtual Desktop using Azure AD Authentication: This article will walk you through the process of configuring single sign-on (SSO) using Azure Active Directory (Azure AD) authentication for Azure Virtual Desktop.
- Azure Virtual Desktop enterprise enrollment considerations: It is important for the cloud platform team to understand the existing enterprise enrollment or Active Directory tenant decisions.
- Device Identities: Learn how to configure and manage device identities in Azure AD.
Azure Virtual Desktop is a managed service that provides a Microsoft control plane for your virtual desktop infrastructure. Identity and access management for Azure Virtual Desktop uses Azure role-based access control (RBAC).
- IDAM: Identity and access management for AVD uses Azure role-based access control (RBAC).
- Enrollment: How to organize your enrollment into subscriptions, management groups, and resource groups.
- Authentication: AVD supports different types of identities depending on which configuration you choose.
- Domain Services: Azure Virtual Desktop requires a hosting strategy for domain services. Choose either AD DS or Azure AD DS.
- Hybrid Identities: Azure Virtual Desktop supports hybrid identities through Azure AD, including those federated using AD FS.
- RBAC Roles: Azure Virtual Desktop uses Azure role-based access control (RBAC) to control access to resources.
[/box]